Many companies and organisation uses Google Workspace as the provider of their productivity and collaboration apps. The Gmail webmail service, Google drive, Google Documents, Google Meet, The calendar and many other apps are simple great tools for small and medium-sized organisations.
Odoo is an open-source suite of business applications that assists companies in managing various aspects of their operations. It’s like a one-stop-shop for business needs and offers modules for everything from project management and inventory control, to customer relationship management (CRM), human resources, accounting, and sales. Odoo is highly customisable, which means businesses can pick and choose which modules they want to use, making it a flexible solution for businesses of all sizes. Its goal is to streamline business processes and improve efficiency. It’s also web-based, which means you can access it from anywhere you have an internet connection.
While setting up Odoo for a company that uses Google Workspace, the IT department raised several concerns about enforcing security policy for accounts on Odoo. It was only natural to look into using Google Workspace as an Identity Provider to Odoo, so I quickly started looking into Single Sign-On (SSO) using SAML for Odoo which I though is supported out of the box. It was quickly obvious that it was not.
After some investigation, I found the auth_server repository from the Odoo Community Association on Github, a non-profit organization helping create lower cost, more successful Odoo solutions faster, with easy access to high quality apps and open upgrades. The auth_server repository contains several modules for Odoo that are related to server side authentication. The module auth_saml allows to deport the management of users and passwords in an external authentication system to provide SSO functionality (Single Sign On) between Odoo and other applications of your ecosystem. Basically it lets users log into Odoo via an SAML2 identity provider. Exactly what we need.
In the following, I will show how to use auth_saml module from OCA to add Google Workspace as a SSO Identity Provider to Odoo.
We start with a Dockerfile. Here we start with the official odoo:16.0 image, then we add the necessary libraries mainly xmlsec1. Then the necessary python packages pysaml2 and xmlsec. Finally we make sure the user running odoo is the user odoo.
# A Dockerfile to add pysaml2 to Odoo 16.
# pysaml2 is important for the auth_saml module.
#
FROM odoo:16.0
USER root
RUN apt-get update
RUN apt-get upgrade -y
RUN apt-get install -y pkg-config libxml2-dev libxmlsec1-dev libxmlsec1-openssl xmlsec1
RUN apt-get install -y python3.9-dev
RUN apt-get install -y build-essential
RUN pip install pysaml2 xmlsec
USER odoo
ENTRYPOINT ["/entrypoint.sh"]
CMD ["odoo"]And the docker-compose file:
---
version: '3.5'
services:
odoo:
image: odoo:16.0
build:
context: .
dockerfile: ./Dockerfile
restart: always
depends_on:
- postgresql
ports:
- "8069:8069"
volumes:
- odoo-data:/var/lib/odoo
- ./extra-addons:/mnt/extra-addons
environment:
- PASSWORD_FILE=/run/secrets/postgresql_password
- HOST=postgresql
- VIRTUAL_HOST=${VIRTUAL_HOST}
- VIRTUAL_PORT=8069
- LETSENCRYPT_HOST=${VIRTUAL_HOST}
- LETSENCRYPT_EMAIL=${LETSENCRYPT_EMAIL}
secrets:
- postgresql_password
networks:
- odoo
- proxy
postgresql:
image: postgres:${POSTGRESQL_VERSION}
environment:
- POSTGRES_USER=odoo
- POSTGRES_DB=postgres
- POSTGRES_PASSWORD_FILE=/run/secrets/postgresql_password
- PGDATA=/var/lib/postgresql/data/pgdata
volumes:
- postgresql-data:/var/lib/postgresql/data/pgdata
secrets:
- postgresql_password
networks:
- odoo
restart: always
volumes:
odoo-data:
postgresql-data:
networks:
odoo:
proxy:
external: true
name: http-proxy_backend
secrets:
postgresql_password:
file: .odoo_pg_passHere docker-compose build the adjusted odoo image from the custom Dockerfile. We mount the local volume ./extra-addons to the /mnt/extra-addons where odoo expects them. In make sure that auth_saml is in our the local ./extra-addson. Then we start docker-compose:
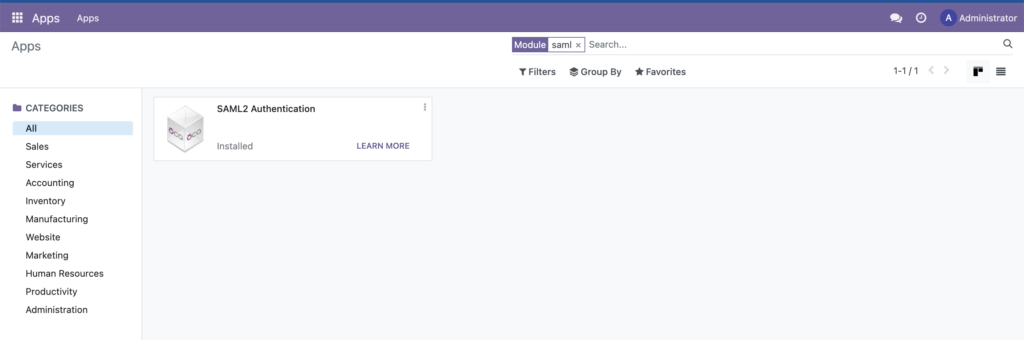
$ docker-compose up -d --buildNow we log to Odoo, and navigate to Apps, and search for the SAML module and install (activate) it.
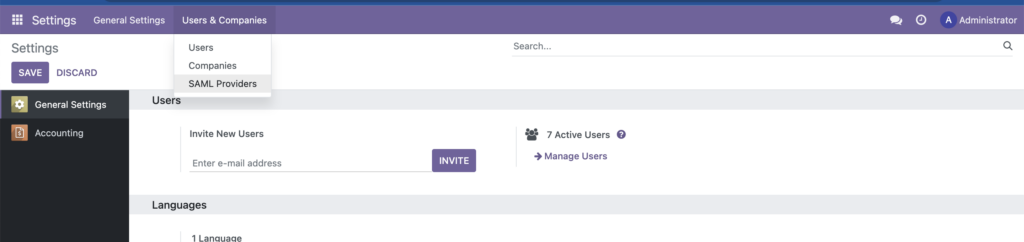
Then we navigate to Settings, then in the Users & Companies menu item we select SAML providers.
Then we add a new SAML provider as in the following screenshot:
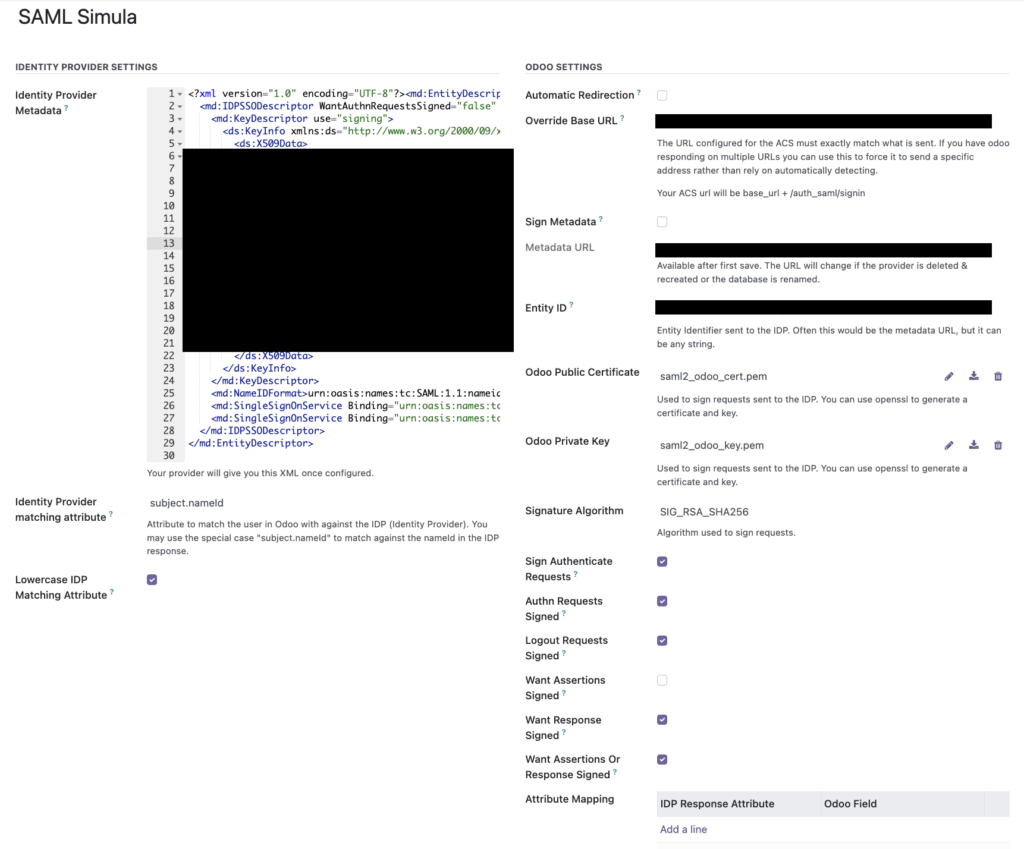
Make sure that “Want Assertions Signed” is kept unchecked.
In parallel on Google Workspace we navigate to admin.google.com then “Web and mobile apps” under the Apps sidebar or simply https://admin.google.com/ac/apps/unified and we click of “Add custom SAML app” and follow the Wizard.
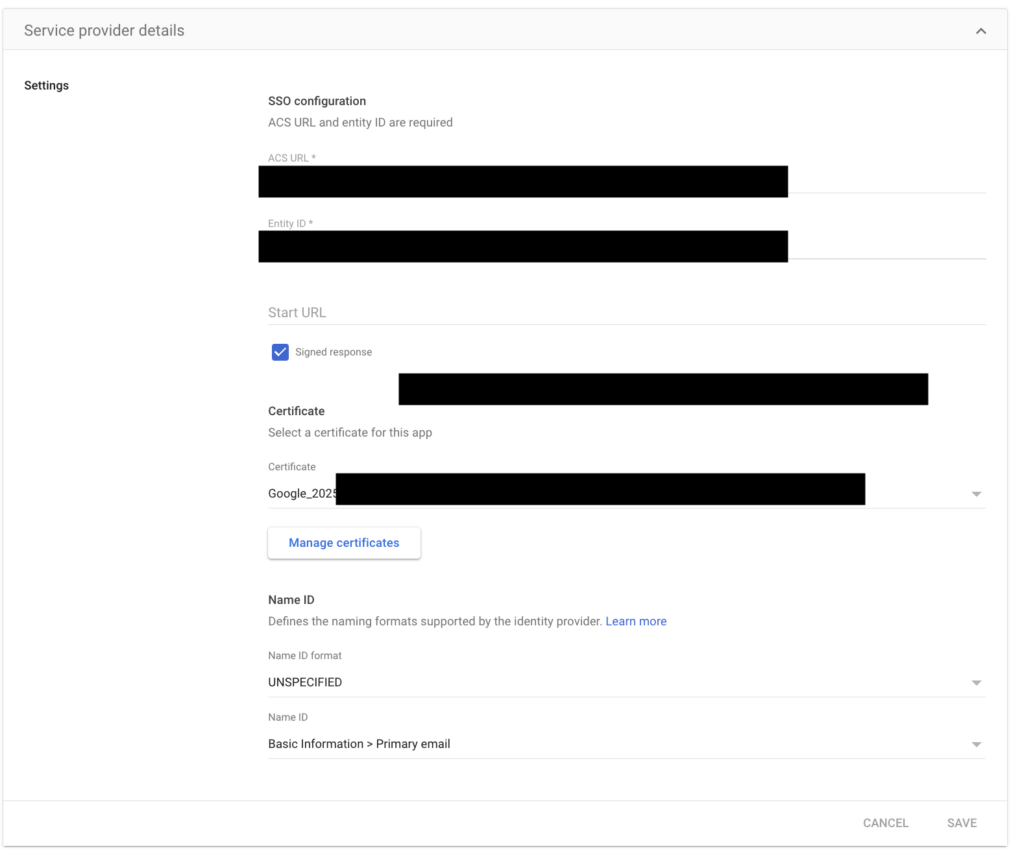
Make sure “Start URL” is kept empty.
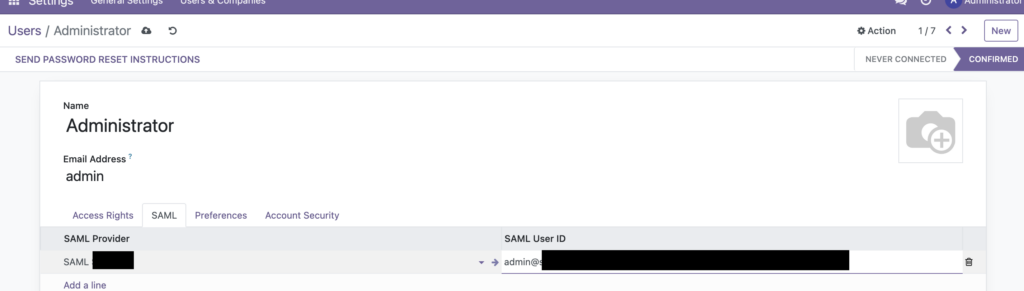
Now let’s enable SAML for a given user. We select the user then we add the SAML provider and connect it to the suitable email defined in Google Workshop:
That’s it…
